Bios 100 final test 2 - Study guides, Class notes & Summaries
Looking for the best study guides, study notes and summaries about Bios 100 final test 2? On this page you'll find 27 study documents about Bios 100 final test 2.
Page 3 out of 27 results
Sort by
-
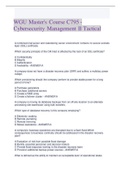
WGU Master's Course C795 2023 - Cybersecurity Management II Tactical
- Exam (elaborations) • 61 pages • 2023
-
- $16.73
- + learn more
WGU Master's Course C795 -2023 Cybersecurity Management II Tactical A combined mail server and calendaring server environment contains no secure sockets layer (SSL) certificate. Which security principle of the CIA triad is affected by the lack of an SSL certificate? A Confidentiality B Integrity C Authentication D Availability - ANSWER A A company does not have a disaster recovery plan (DRP) and suffers a multiday power outage. Which provisioning should the company perform to provide...

-
WGU Master's Course C795 - Cybersecurity Management II Tactical
- Exam (elaborations) • 58 pages • 2022
-
Available in package deal
-
- $16.49
- 1x sold
- + learn more
A combined mail server and calendaring server environment contains no secure sockets layer (SSL) certificate. Which security principle of the CIA triad is affected by the lack of an SSL certificate? A Confidentiality B Integrity C Authentication D Availability Correct answer- A A company does not have a disaster recovery plan (DRP) and suffers a multiday power outage. Which provisioning should the company perform to provide stable power for a long period of time? A Purchase gen...

-
CISSP_ CBK _Review Final Exam
- Exam (elaborations) • 53 pages • 2021
-
- $17.49
- + learn more
CISSP CBK Review Final Exam CISSP CBK Review Page 1 1. A risk is the likelihood of a threat source taking advantage of a vulnerability to an information system. Risks left over after implementing safeguards is known as: A. Leftover risks. B. Residual risks. C. Remaining risks. D. Exposures. 2. Copyright provides what form of protection: A. Protects an author’s right to distribute his/her works. B. Protects information that provides a competitive advantage. C. Protects the right of an...

-
HPE ProLiant Questions and Answers, Lab Reports for Mathematics 3.8 (14) Refer to the exhibit of an internal view of the HPE ProLiant WS460c Graphics Server Blade.- HPE Smart Array P244br ControllerA ProLiant BL server supports a maximum of ____ memory.-
- Exam (elaborations) • 4 pages • 2023
-
- $10.99
- + learn more
HPE ProLiant Questions and Answers, Lab Reports for Mathematics 3.8 (14) Refer to the exhibit of an internal view of the HPE ProLiant WS460c Graphics Server Blade.- HPE Smart Array P244br ControllerA ProLiant BL server supports a maximum of ____ memory.- 2 TBThe internal components of the HPE ProLiant DL180 Gen10 Server are shown below.- Type-a Smart Array ConnectorA customer notices the UID LED is flashing blue. What does this indicate- The system is being remotely managedWhich server suppor...

-
HPE ProLiant Questions and Answers, Lab Reports for Mathematics 3.8 (14) Refer to the exhibit of an internal view of the HPE ProLiant WS460c Graphics Server Blade.- HPE Smart Array P244br ControllerA ProLiant BL server supports a maximum of ____ memory.-
- Exam (elaborations) • 4 pages • 2023
-
- $15.99
- + learn more
HPE ProLiant Questions and Answers, Lab Reports for Mathematics 3.8 (14) Refer to the exhibit of an internal view of the HPE ProLiant WS460c Graphics Server Blade.- HPE Smart Array P244br ControllerA ProLiant BL server supports a maximum of ____ memory.- 2 TBThe internal components of the HPE ProLiant DL180 Gen10 Server are shown below.- Type-a Smart Array ConnectorA customer notices the UID LED is flashing blue. What does this indicate- The system is being remotely managedWhich server suppor...

-
CISSP CBK Review Final Exam; Test bank (all answered correctly)
- Exam (elaborations) • 53 pages • 2021
-
- $10.49
- + learn more
CISSP CBK Review Final Exam CISSP CBK Review Page 1 1. A risk is the likelihood of a threat source taking advantage of a vulnerability to an information system. Risks left over after implementing safeguards is known as: A. Leftover risks. B. Residual risks. C. Remaining risks. D. Exposures. 2. Copyright provides what form of protection: A. Protects an author’s right to distribute his/her works. B. Protects information that provides a competitive advantage. C. Protects the right of a...

-
BIOS 242 Midterm plus Final Exam with 100% Correct Answers
- Exam (elaborations) • 8 pages • 2021
- Available in package deal
-
- $18.49
- + learn more
BIOS 242 Midterm plus Final Exam with 100% Correct Answers Question: Which of the following is ‘not’ a microscopic organism that Leewenhook was able to observe under the microscope he constructed in 1674? Question: Which of the following is INCORRECT regarding Archaea? Question: What is the name for sphere-shaped bacterial cells? Question: Where do you find genetic material in a prokaryotic cell? Question: Which of the following statements is INCORRECT regarding glycocalyces? Question:...

Study stress? For sellers on Stuvia, these are actually golden times. KA-CHING! Earn from your study resources too and start uploading now. Discover all about earning on Stuvia


