Failures of siem - Study guides, Class notes & Summaries
Looking for the best study guides, study notes and summaries about Failures of siem? On this page you'll find 53 study documents about Failures of siem.
Page 3 out of 53 results
Sort by

-
(ISC)2 Certified In Cybersecurity - Exam Prep Questions with 100% Correct Answers | Verified | Updated 2024.
- Exam (elaborations) • 65 pages • 2024
-
- $18.49
- + learn more
(ISC)2 Certified In Cybersecurity - Exam Prep Questions with 100% Correct Answers | Verified | Updated 2024. Document specific requirements that a customer has about any aspect of a vendor's service performance. A) DLR B) Contract C) SLR D) NDA C) SLR (Service-Level Requirements) _________ identifies and triages risks. Risk Assessment _________ are external forces that jeopardize security. Threats _________ are methods used by attackers. Threat Vectors _________ are the combina...

-
SECURITY+ SY0-601 STUDY SET from Mike Myer's Book
- Exam (elaborations) • 41 pages • 2022
-
- $13.99
- 1x sold
- + learn more
SECURITY+ SY0-601 STUDY SET from Mike Myer's BookSECURITY+ SY0-601 STUDY SET from Mike Myer's Book __________________ is defined as using and manipulating human behavior to obtain a required result. It typically involves NON-TECHNICAL methods of attempting to gain unauthorized access to a system or network. Correct answer- Social engineering Through social engineering, an attacker might easily lead a user to reveal her account password or to provide personal information that mi...

-
CISA Exam 388 Questions with Verified Answers,100% CORRECT
- Exam (elaborations) • 90 pages • 2024
-
- $12.99
- + learn more
CISA Exam 388 Questions with Verified Answers Which of the following controls will MOST effectively detect the presence of bursts of errors in network transmissions? a. Parity check b. Echo check c. Block sum check d. Cyclic redundancy check - CORRECT ANSWER d. Cyclic redundancy check Which of the following issues associated with a data center's closed circuit television (CCTV) surveillance cameras should be of MOST concern to an IS auditor? A. CCTV recordings are not regularly revi...

-
ISC2 (ISC)2 Certified in Cybersecurity - Exam Prep
- Exam (elaborations) • 73 pages • 2023
-
- $17.00
- + learn more
ISC2 (ISC)2 Certified in Cybersecurity - Exam Prep ISC2 (ISC)2 Certified in Cybersecurity - Exam Prep Document specific requirements that a customer has about any aspect of a vendor's service performance. A) DLR B) Contract C) SLR D) NDA C) SLR (Service-Level Requirements) _________ identifies and triages risks. Risk Assessment _________ are external forces that jeopardize security. Threats _________ are methods used by attackers. Threat Vectors _________ are the combinati...

-
Security and Operations and Incident Response Exam 134 Questions with Verified Answers,100% CORRECT
- Exam (elaborations) • 32 pages • 2024
-
- $11.49
- + learn more
Security and Operations and Incident Response Exam 134 Questions with Verified Answers Eren needs to establish a tool that can let him see all of the systems that a given IP address connects to and how much data that IP received by port and protocol. Which is NOT a suitable tool for that need? A. NetFlow B. IPSec C. IPFIX D. sFlow - CORRECT ANSWER B. IPSec; IPSec is not used to capture network flows. A system that Mark takes responsibility for crashed and he guesses that a malware iss...
-
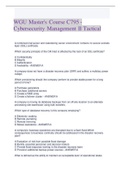
WGU Master's Course C795 2023 - Cybersecurity Management II Tactical
- Exam (elaborations) • 61 pages • 2023
-
- $16.73
- + learn more
WGU Master's Course C795 -2023 Cybersecurity Management II Tactical A combined mail server and calendaring server environment contains no secure sockets layer (SSL) certificate. Which security principle of the CIA triad is affected by the lack of an SSL certificate? A Confidentiality B Integrity C Authentication D Availability - ANSWER A A company does not have a disaster recovery plan (DRP) and suffers a multiday power outage. Which provisioning should the company perform to provide...

-
WGU C838 MANAGING CLOUD SECURITY FINAL EXAM TEST BANK 400 QUESTIONS AND ANSWERS LATEST 2023/2024
- Exam (elaborations) • 55 pages • 2023
-
Available in package deal
-
- $15.99
- + learn more
WGU C838 MANAGING CLOUD SECURITY What NIST publication number defines cloud computing? - ANSWER- 800-145 What ISO/IEC standard provides information on cloud computing? - ANSWER- 17788 What is cloud bursting? - ANSWER- Ability to increase available cloud resources on demand What are 3 characteristics of cloud computing? - ANSWER- Elasticity Simplicity Scalability What is a cloud customer? - ANSWER- Anyone purchasing cloud services What is a cloud ...

-
Domain 4 CISA Exam 325 Questions with Verified Answers,100% CORRECT
- Exam (elaborations) • 93 pages • 2024
-
- $12.99
- + learn more
Domain 4 CISA Exam 325 Questions with Verified Answers what identifies and locates assets within a limited radius? - CORRECT ANSWER RFID- Radio Frequency Identification What uses radio waves to identify tagged objects? - CORRECT ANSWER RFID- Radio Frequency Identification In (RFID) Radio Frequency Identification, uses radio waves to identify TAGGED objects. What is included in a tag? - CORRECT ANSWER A tag includes a microchip and antenna. Microchip stores info and Antenna transmits inf...

-
CySA+ Final Exam Graded A+
- Exam (elaborations) • 9 pages • 2022
-
- $9.49
- + learn more
Despite operating a patch management program, your company has been exposed to several attacks over the last few months. You have drafted a policy to require a lessons-learned incident report be created to review the historical attacks and to make this analysis a requirement following future attacks. How can this type of control be classified? - ANSWER Administrative/Corrective A bespoke application used by your company has been the target of malware. The developers have created signatures fo...

-
CCSP 2020 BEST EXAM STUDY 2021
- Exam (elaborations) • 157 pages • 2022
-
- $20.99
- 1x sold
- + learn more
What type of solutions enable enterprises or individuals to store data and computer files on the Internet using a storage service provider rather than keeping the data locally on a physical disk such as a hard drive or tape backup? A. Online backups B. Cloud backup solutions C. Removable hard drives D. Masking Correct answer- B When using an infrastructure as a service (IaaS) solution, which of the following is not an essential benefit for the customer? A. Removing the nee...

That summary you just bought made someone very happy. Also get paid weekly? Sell your study resources on Stuvia! Discover all about earning on Stuvia


